The latest report from business intelligence provider visiongain offers comprehensive analysis of the global Cyber Security market. Visiongain assesses that this market will generate revenues of $83.5bn in 2017.
With the growing prevalence of cyber attacks, and the proliferation of cloud, mobility, and bring-your-own-device (BYOD), cyber security is crucial for all points in the network. Cyber security threats and vulnerabilities can change from day to day, and even hour to hour. Effective steps for managing cyber risks today are unlikely to suffice for very long, and thus maintaining security in a wireless environment is challenging for most vendors in the ecosystem.
Cyber threats affect more than just the Information Technology (IT) infrastructure of a company. These threats can cause disruptions to the entire network and impact principal business functions and mission.
Several organizations integrate cyber defence with traditional security activities, such as physical and personnel security as part of an overarching effort to protect business operations from both external and internal threats. Furthermore, cyber security activities are now being prioritized and aligned to strategic business activities to minimize the damage of IT resources.
You need to read visiongain’s objective analysis of how this evolving cyber security landscape will impact your company and the industry more broadly. How are you and your company reacting to the changing cyber threats? Are you sufficiently informed?
How this report will benefit you
Read on to discover how you can exploit the future business opportunities emerging in the cyber security sector. Visiongain’s new study tells you and tells you NOW.
In this brand new report you find 261 in-Depth tables, charts and graphs– all unavailable elsewhere.
The 289 page report provides clear detailed insight into the global Cyber Security market. Discover the key drivers and challenges affecting the market.
By ordering and reading our brand new report today you stay better informed and ready to act.
Report Scope
Global Cyber Security Market Forecasts From 2017-2027
Regional Cyber Security Market Forecasts From 2017-2027
• Asia-Pacific Cyber Security Market Forecast From 2017-2027
• Europe Cyber Security Market Forecast From 2017-2027
• Latin America Cyber Security Market Forecast From 2017-2027
• Middle East and Africa Cyber Security Market Forecast From 2017-2027
• North America Cyber Security Market Forecast From 2017-2027
Country Cyber Security Market Forecasts From 2017-2027
• U.S. Cyber Security Market Forecast From 2017-2027
• UK Cyber Security Market Forecast From 2017-2027
• France Cyber Security Market Forecast From 2017-2027
• Russia Cyber Security Market Forecast From 2017-2027
• China Cyber Security Market Forecast From 2017-2027
• Japan Cyber Security Market Forecast From 2017-2027
• South Korea Cyber Security Market Forecast From 2017-2027
• Israel Cyber Security Market Forecast From 2017-2027
• Saudi Arabia Cyber Security Market Forecast From 2017-2027
Cyber Security Solution Submarket Forecasts From 2017-2027
• Risk and Compliance Management Cyber Security Market Forecast From 2017-2027
• Unified Threat Management (UTM) Cyber Security Market Forecast From 2017-2027
• Security Incident Management Cyber Security Market Forecast From 2017-2027
• Identity and Access Management (IAM) Cyber Security Market Forecast From 2017-2027
• Encryption Cyber Security Market Forecast From 2017-2027
• Intrusion Prevention Systems (IPSs) Cyber Security Market Forecast From 2017-2027
• Others Cyber Security Market Forecast From 2017-2027
Cyber Security Service Submarket Forecasts From 2017-2027
• Professional Services Cyber Security Market Forecast From 2017-2027
• Managed Services Cyber Security Market Forecast From 2017-2027
Cyber Security Deployment Type Submarket Forecasts From 2017-2027
• On-Premises Cyber Security Market Forecast From 2017-2027
• Cloud Cyber Security Market Forecast From 2017-2027
Cyber Security User Type Submarket Forecasts From 2017-2027
• SMEs Cyber Security Market Forecast From 2017-2027
• Large Enterprises Cyber Security Market Forecast From 2017-2027
Cyber Security Industry Vertical Submarket Forecasts From 2017-2027
• Aerospace and Defence Cyber Security Market Forecast From 2017-2027
• BFSI Cyber Security Market Forecast From 2017-2027
• Public Sector Cyber Security Market Forecast From 2017-2027
• Retail Cyber Security Market Forecast From 2017-2027
• Healthcare Cyber Security Market Forecast From 2017-2027
• IT and Telecom Cyber Security Market Forecast From 2017-2027
• Energy and Utilities Cyber Security Market Forecast From 2017-2027
• Manufacturing Cyber Security Market Forecast From 2017-2027
• Others Cyber Security Market Forecast From 2017-2027
Profiles Of The Leading Cyber Security Companies With Market Share Of Th Leading 6 Companies
• Dell EMC
• Cisco Systems
• FireEye Inc.
• Hewlett Packard Enterprises (HPE)
• IBM Corporation
• Sophos Ltd.
• Intel Corporation
• Symantec Corporation
• TrendMicro Inc.
• Verizon Communications
• Lockheed Martin Corporation
• Northrop Grumman Corporation
• Palo Alto Networks Inc.
Who should read this report?
• Cyber security companies
• Information security specialists
• Cloud computing companies
• Internet of things companies
• Hardware providers
• Software vendors
• Managed services companies
• Industrial control system companies
• Large enterprises
• It contractors
• IT departments
• CEOs,
• Security vendors
• Heads of strategic development
• Marketing staff
• Market analysts
• Procurement staff
• Company managers
• Industry administrators
• Industry associations
• Company procurement departments
• Consultants
• Managers
• Governmental departments & agencies
• Business development managers
• Investors
• Banks
Visiongain’s study is intended for anyone requiring commercial analyses for the Cyber Security market and leading companies. You find data, trends and predictions.
Buy our report today Cyber Security Market Analysis : Forecasts by Solutions (Risk and Compliance Management, Unified Threat Management (UTM), Security Incident Management, Identity and Access Management (IAM), Encryption, Intrusion Prevention Systems (IPS), Others), by Services (Professional Services, Managed Services), by Deployment Type (On-Premises, Cloud), by User Type (SMEs, Large Enterprises), by Industry Vertical (Aerospace and Defence, BFSI, Public Sector, Retail, Healthcare, IT and Telecom, Energy and Utilities, Manufacturing, Others).
Avoid missing out by staying informed – get our report now.
Visiongain is a trading partner with the US Federal Government
CCR Ref number: KD4R6
1. Report Overview
1.1 Global Cyber Security Market Overview
1.2 Global Cyber Security Market Segmentation
1.3 Why You Should Read This Report
1.4 How this Report Delivers
1.5 Key Questions Answered by This Analytical Report Include
1.6 Who is This Report For?
1.7 Methodology
1.7.1 Primary Research
1.7.2 Secondary Research
1.7.3 Market Evaluation & Forecasting Methodology
1.8 Frequently Asked Questions (FAQ)
1.9 Associated Visiongain Reports
1.10 About Visiongain
2. Introduction to Cyber Security Market
2.1 Cyber Security Market Overview
2.1.1. Cyber Security Market Definition
2.2 Cyber Security Submarket
2.2.1 Cyber Security, By Solution
2.2.2 Cyber Security, By Services
2.2.3 Cyber Security, By Deployment Type
2.2.4 Cyber Security, By User Type
2.2.5 Cyber Security, By Industry Vertical
2.3 Most Common Methods of Cyber Attacks
2.4 Main Objectives of Cyber Attackers
2.5 Most Important Mechanisms of Cyber Attacks
2.6 Stage of Cyber Attacks
2.7 Recent Notable Cyber Attacks & Incidents
3. Global Cyber Security Market Dynamics
3.1 Cyber Security Market Drivers
3.1.1 Rise In Malware And Phishing Threats Among Enterprises
3.1.2 Increasing Adoption Of IoT And BYOD Trend
3.1.3 Growing Demand For Cloud-Based Cyber Security Solutions
3.2 Cyber Security Market Restraints
3.2.1 Increase In Adoption Of Mobile Device Applications And Platforms
3.2.2 Need For Strong Authentication Methods
3.2.3 Transformation In Traditional Anti-Virus Software Industry
3.3 Cyber Security Market Challenges
3.3.1 Budget Constraints Among Organizations
3.3.2 Lack Of Security Awareness Among Enterprises
4. Value Chain Analysis
4.1 Security Solution Provider
4.2 Cloud Service Providers
4.3 End-Users
5. Porter’s Five Forces Analysis
5.1 Moderate Bargaining Power Of Suppliers
5.2 High Threat Of New Entrants
5.3 Moderate Threat Of Substitutes
5.4 High Competitive Rivalry
5.5 Moderate Bargaining Power Of Buyers
6. The Global Cyber Security Solution Submarket Market Forecasts 2017-2027
6.1 Global Cyber Security Solution Submarket By Regional Forecast 2017-2027
6.2 Regional Cyber Security Risk And Compliance Management Solution Submarket Forecast 2017-2027
6.3 Regional Cyber Security UTM Solution Submarket Forecast 2017-2027
6.4 Regional Cyber Security Security Incident Management Solution Submarket Forecast 2017-2027
6.5 Regional Cyber Security Iam Submarket Forecast 2017-2027
6.6 Regional Cyber Security Encryption Solution Submarket Forecast 2017-2027
6.7 Regional Cyber Security Ips Solution Submarket Forecast 2017-2027
6.8 Regional Cyber Security Other Solution Submarket Forecast 2017-2027
6.9 Global Cyber Security Solution Submarket Share Forecast 2017-2027
6.10 Risk And Compliance Management Cyber Security Market 2017-2027
6.10.1 Risk And Compliance Management Cyber Security Key Drivers & Opportunities
6.10.2 Risk And Compliance Management Cyber Security Market Size And Forecast
6.11 Unified Threat Management Cyber Security Market 2017-2027
6.11.1 Utm Cyber Security Key Drivers And Opportunities
6.11.2 Utm Cyber Security Market Size And Forecast
6.12 Security Incident Management Cyber Security Market 2017-2027
6.12.1 Security Incident Management Cyber Security Key Drivers And Opportunities
6.12.2 Security Incident Management Cyber Security Market Size And Forecast
6.13 Identity And Access Management Cyber Security Market 2017-2027
6.13.1 Identity And Access Management Cyber Security Key Drivers And Opportunities
6.13.2 Identity And Access Management Cyber Security Market Size And Forecast
6.14 Encryption Cyber Security Market 2017-2027
6.14.1 Encryption Cyber Security Key Drivers And Opportunities
6.14.2 Encryption Cyber Security Market Size And Forecast
6.15 Intrusion Prevention Systems Cyber Security Market 2017-2027
6.15.1 Intrusion Prevention Systems Cyber Security Key Drivers And Opportunities
6.15.2 Intrusion Prevention Systems Cyber Security Market Size And Forecast
6.16 Others Cyber Security Market 2017-2027
6.16.1 Others Cyber Security Key Drivers And Opportunities
6.16.2 Others Cyber Security Market Size And Forecast
7. The Global Cyber Security Services Market Forecasts 2017-2027
7.1 Global Cyber Security Services Submarket By Regional Market Forecast 2017-2027
7.2 Regional Cyber Security Professional Services Submarket Forecast 2017-2027
7.3 Regional Cyber Security Managed Services Submarket Forecast 2017-2027
7.4 Global Cyber Security Services Submarket Share Forecast 2017-2027
7.5 Professional Services Cyber Security Market 2017-2027
7.5.1 Professional Services Cyber Security Key drivers and opportunities
7.5.2 Professional Services Cyber Security Market size and forecast
7.6 Managed Services Cyber Security Market 2017-2027
7.6.1 Managed Services Cyber Security Key drivers and opportunities
7.6.2 Managed Services Cyber Security Market size and forecast
8. The Global Cyber Security Deployment Type Market Forecasts 2017-2027
8.1 Global Cyber Security Deployment Type Submarket by Regional Market Forecast 2017-2027
8.2 Regional Cyber Security Cloud Based Submarket Forecast 2017-2027
8.3 Regional Cyber Security On-Premises Submarket Forecast 2017-2027
8.4 Global Cyber Security Deployment Type Submarket Share Forecast 2017-2027
8.5 Cloud Based Cyber Security Market 2017-2027
8.5.1 Cloud Based Cyber Security Key Drivers & Opportunities
8.5.2 Cloud Based Cyber Security Market size and forecast
8.6 On-Premises Cyber Security Market 2017-2027
8.6.1 On-Premises Cyber Security Key Drivers & Opportunities
8.6.2 On-Premises Cyber Security Market size and forecast
9. The Global Cyber Security User Type Market Forecasts 2017-2027
9.1 Global Cyber Security User Type Submarket By Regional Market Forecast 2017-2027
9.2 Regional Cyber Security Large Enterprise Submarket Forecast 2017-2027
9.3 Regional Cyber Security SMEs Submarket Forecast 2017-2027
9.4 Global Cyber Security User Type Submarket Share Forecast 2017-2027
9.5 Large Enterprises Cyber Security Market 2017-2027
9.5.1 Large Enterprises Cyber Security Key Drivers & Opportunities
9.5.2 Large Enterprises Cyber Security Market size and forecast
9.6 SMEs Cyber Security Market 2017-2027
9.6.1 SMEs Cyber Security Key Drivers & Opportunities
9.6.2 SMEs Cyber Security Market size and forecast
10. The Global Cyber Security Industry Vertical Market Forecasts 2017-2027
10.1 Global Cyber Security Industry Vertical Submarket Forecast 2017-2027
10.2 Global Cyber Security Industry Vertical Submarket By Regional Market Forecast 2017-2027
10.3 Regional Cyber Security Aerospace & Defence Submarket Forecast 2017-2027
10.4 Regional Cyber Security BFSI Submarket Forecast 2017-2027
10.5 Regional Cyber Security Public Sector Submarket Forecast 2017-2027
10.6 Regional Cyber Security Retail Submarket Forecast 2017-2027
10.7 Regional Cyber Security Healthcare Submarket Forecast 2017-2027
10.8 Regional Cyber Security IT & Telecom Submarket Forecast 2017-2027
10.9 Regional Cyber Security Energy & Utilities Submarket Forecast 2017-2027
10.10 Regional Cyber Security Manufacturing Submarket Forecast 2017-2027
10.11 Regional Cyber Security Other Industry Vertical Submarket Forecast 2017-2027
10.12 Global Cyber Security Industry Vertical Submarket Share Forecast 2017-2027
10.13 Aerospace & Defense Cyber Security Market 2017-2027
10.13.1 Aerospace & Defense Cyber Security Key Drivers & Opportunities
10.13.2 Aerospace & Defense Cyber Security Market size and forecast
10.14 BFSI Cyber Security Market 2017-2027
10.14.1 BFSI Cyber Security Key Drivers & Opportunities
10.14.2 BFSI Cyber Security Market size and forecast
10.15 Public Sector Cyber Security Market 2017-2027
10.15.1 Public Sector Cyber Security Key Drivers & Opportunities
10.15.2 Public Sector Cyber Security Market size and forecast
10.16 Retail Cyber Security Market 2017-2027
10.16.1 Retail Cyber Security Key Drivers & Opportunities
10.16.2 Retail Cyber Security Market size and forecast
10.17 Healthcare Cyber Security Market 2017-2027
10.17.1 Healthcare Cyber Security Key Drivers & Opportunities
10.17.2 Healthcare Cyber Security Market size and forecast
10.18 IT & Telecom Cyber Security Market 2017-2027
10.18.1 IT & Telecom Cyber Security Key Drivers & Opportunities
10.18.2 IT & Telecom Cyber Security Market size and forecast
10.19 Energy & Utilities Cyber Security Market 2017-2027
10.19.1 Energy & Utilities Cyber Security Key Drivers & Opportunities
10.19.2 Energy & Utilities Cyber Security Market size and forecast
10.20 Manufacturing Cyber Security Market 2017-2027
10.20.1 Manufacturing Cyber Security Key Drivers & Opportunities
10.20.2 Manufacturing Cyber Security Market size and forecast
10.21 Others Cyber Security Market 2017-2027
10.21.1 Others Cyber Security Key Drivers & Opportunities
10.21.2 Others Cyber Security Market size and forecast
11. Regional Cyber Security Market Forecasts 2017-2027
11.1 North America Cyber Security Market 2017-2027
11.2 Europe Cyber Security Market 2017-2027
11.3 Asia-Pacific Cyber Security Market 2017-2027
11.4 Latin America, Middle East & Africa (LAMEA) Cyber Security Market 2017-2027
12. Country Level Cyber Security Market Forecast 2017-2027
12.1 Leading 9 National Cyber Security Markets Share Forecast 2017-2027
12.1.1 Cyber Security in China
12.1.2 Chinese Military Cyber Strategy
12.1.3 Chinese National Cyber Strategy
12.1.4 China Cyber Security Market Drivers & Restraints
12.2 France Cyber Security
12.2.1 Cyber Security in France
12.2.2 France Cyber Security Market Drivers & Restraints
12.3 Japan Cyber Security Market Forecast 2017-2027
12.3.1 Cyber Security in Japan
12.3.2 Japan Cyber Security Market Drivers & Restraints
12.4 Russia Cyber Security Market Forecast 2017-2027
12.4.1 Cyber Security in Russia
12.4.2 Russia Cyber Security Market Drivers & Restraints
12.5 United States Cyber Security Market Forecast 2017-2027
12.5.1 Cyber Security in U.S.
12.5.2 U.S. Cyber Security Market Drivers & Restraints
12.5.3 United States Cyber Security Market Contracts & Programmes
12.5.4 United States Federal Government’s Budget for Cyber Security
12.5.5 Essential Components of the U.S. Cyber Security Power
12.6 United Kingdom Cyber Security Market Forecast 2017-2027
12.6.1 United Kingdom Cyber Security Market Drivers & Restraints
12.6.2 United Kingdom Cyber Security Export
12.7 South Korea Cyber Security Market Forecast 2017-2027
12.7.1 Cyber Security in South Korea
12.7.2 South Korea Cyber Security Market Drivers & Restraints
12.8 Israel Cyber Security Market Forecast 2017-2027
12.8.1 Israeli Defence Contracts Value 2010-2016
12.8.2 Cyber Security in Israel
12.8.3 Israel Cyber Security Market Drivers & Restraints
12.9 Saudi Arabia Cyber Security Market Forecast 2017-2027
12.9.1 Cyber Security in Saudi Arabia
12.9.2 Saudi Arabia Cyber Security Market Drivers & Restraints
13. SWOT Analysis of the Cyber Security Market 2017-2027
14. Leading Cyber Security Companies
14.1 Market Share Analysis, 2016 (%)
14.2 Dell EMC
14.2.1 Dell EMC Company Overview
14.2.2 Dell EMC Company Snapshot
14.2.3 Dell EMC Business Performance
14.2.4 Dell EMC Key Developments
14.3 Cisco Systems
14.3.1 Cisco Systems Company Overview
14.3.2 Cisco Systems Company Snapshot
14.3.3 Cisco Systems Business Performance
14.3.4 Cisco Systems Key Developments
14.4 FireEye Incorporated
14.4.1 FireEye Incorporated Company Overview
14.4.2 FireEye Incorporated Company Snapshot
14.4.3 FireEye Incorporated Key Developments
14.5 Hewlett Packard Enterprise (HPE)
14.5.1 Hewlett Packard Enterprise (HPE) Company Overview
14.5.2 Hewlett Packard Enterprise (HPE) Company Snapshot
14.5.3 Hewlett Packard Enterprise (HPE) Key Developments
14.6 International Business Machine (IBM) Corporation
14.6.1 International Business Machine (IBM) Corporation Company Overview
14.6.2 IBM Corporation Company snapshot
14.6.3 International Business Machine (IBM) Corporation Key Developments
14.7 Sophos Ltd.
14.7.1 Sophos Ltd. Company Overview
14.7.2 Sophos Ltd. Company Snapshot
14.7.3 Sophos Ltd. Key Developments
14.8 Intel Corporation
14.8.1 Intel Corporation Company Overview
14.8.2 Intel Corporation Company Snapshot
14.8.3 Intel Corporation Key Developments
14.9 Symantec Corporation
14.9.1 Symantec Corporation Company Overview
14.9.2 Symantec Corporation Company Snapshot
14.9.3 Symantec Key Developments
14.10 Trend Micro
14.10.1 Trend Micro Company Overview
14.10.2 Trend Micro Company Snapshot
14.10.3 Trend Micro Key Developments
14.11 Verizon Communications
14.11.1 Verizon Communications Company Overview
14.11.2 Verizon Communications Company Snapshot
14.11.3 Verizon Communications Key Developments
14.12 Lockheed Martin Corporation
14.12.1 Lockheed Martin Corporation Company Overview
14.12.2 Lockheed Martin Corporation Company Snapshot
14.13 Northrop Grumman Corporation
14.13.1 Northrop Grumman Corporation Company Overview
14.13.2 Northrop Grumman Corporation Company Snapshot
14.14 Palo Alto Networks, Inc.
14.14.1 Palo Alto Networks, Inc. Company Overview
14.14.2 Palo Alto Networks, Inc Company Snapshot
14.15 Other Companies Involved in the Cyber Security Market 2017
15. Conclusions & Predictions
15.1 Conclusion
15.2 Predictions
15.3 Key Findings
15.3.1 Factors impacting the market
15.3.2 Winning strategies
15.3.3 Growth Potential of Cyber Security
16. Glossary
List of Tables
Table 1.1 Global Cyber Security Market by Regional Market Forecast 2017-2027 (US$m, YOY %, Cumulative)
Table 1.2 Example of Leading National Cyber Security Market Forecast by Submarket 2017-2027 (US$m, AGR%, Cumulative)
Table 2.1 Methods of Cyber Attacks (Type, Description)
Table 2.2 Objectives of Cyber Attackers (Type, Description)
Table 2.3 Mechanisms of Cyber Attacks (Type, Description)
Table 2.4 Notable Cyber Attacks and Incidents worldwide 2016-2017 (Date, Name of the Attack / Incident, Description)
Table 2.5 Notable Cyber Attacks and Incidents Worldwide 1988-2017 (Date, Name of the Attack / Incident, Description)
Table 6.1 Global Cyber Security Solution Submarket Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 6.2 Global Cyber Security Solution Submarket by Regional Market Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 7.1 Global Cyber Security Services Submarket Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 7.2 Global Cyber Security Services Submarket By Regional Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 8.1 Global Cyber Security Submarket by Deployment Type 2017-2027 (US$m, AGR%, CAGR%)
Table 8.2 Global Cyber Security Submarket by Deployment Type Regional Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 9.1 Global Cyber Security Submarket by User Type 2017-2027 (US$m, AGR%, CAGR%)
Table 9.2 Global Cyber Security Submarket by User Type Regional Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 10.1 Global Cyber Security Industry Vertical Submarket by Industry Vertical 2017-2027 (US$m, AGR%, CAGR%)
Table 10.2 Global Cyber Security Industry Vertical Submarket by Regional Market Forecast 2017-2027 (US$m, AGR%, CAGR%)
Table 12.1 Global Cyber Security Submarket Forecast By Country Level 2017-2027 (US$m, AGR%, CAGR%)
Table 12.2 Leading 9 National Cyber Security Markets CAGR Forecast 2017-2027 (CAGR %)
Table 12.3 China Cyber Security Market Drivers & Restraints 2017
Table 12.4 France Cyber Security Market Drivers & Restraints 2017
Table 12.5 Japan Cyber Security Market Drivers & Restraints 2017
Table 12.6 Russia Cyber Security Market Drivers & Restraints 2017
Table 12.7 U.S. Cyber Security Market Drivers & Restraints 2017
Table 12.8 U.S. Cyber Security Market Major Contracts & Programmes 2015-2018 (Date, Organisation, Contractor, Value US$m, Product, Details)
Table 12.9 U.S. Federal Government’s Global Budget for Cyber Security 2013-2016 (US$m)
Table 12.10 U.S. Government and Military Cyber Security Organisations’ Role (US Code, Title, Focus, Organisation, Role)
Table 12.11 UK Cyber Security Market Drivers & Restraints 2017
Table 12.12 UK National Cyber Security Programme Spending by Segments Share 2016-2017 (US$m)
Table 12.13 UK Cyber Security Export in the Security Sector 2014-2017 (US$m, AGR %)
Table 12.14 South Korea Cyber Security Market Drivers & Restraints 2017
Table 12.15 Israeli Defence Contracts Total Value 2010-2016 (US$m)
Table 12.16 Israel Cyber Security Market Drivers & Restraints 2017
Table 12.17 Saudi Arabia Cyber Security Market Drivers & Restraints 2017
Table 13.1 Global Cyber Security Market SWOT Analysis 2017-2027
Table 14.1 Dell EMC Company Snapshot
Table 14.2 Dell EMC Key Developments
Table 14.3 Cisco Systems Company Snapshot
Table 14.4 Cisco Systems Key Developments
Table 14.5 FireEye Incorporated Company Snapshot
Table 14.6 FireEye Incorporated Key Developments
Table 14.7 Hewlett Packard Enterprises (HPE) Company Snapshot
Table 14.8 Hewlett Packard Enterprises (HPE) Key Developments
Table 14.9 Selected Hewlett-Packard (HP) Cyber Security Contracts / Projects / Programmes (Date, Country, Value US$m, Details)
Table 14.10 IBM Corporation Company Snapshot
Table 14.11 IBM Corporation Key Developments
Table 14.12 Selected IBM Corporation Cyber Security Contracts / Projects / Programmes (Date, Country, Value US$m, Product, Details)
Table 14.13 Sophos Ltd. Company Snapshot
Table 14.14 Sophos Ltd. Key Developments
Table 14.15 Intel Corporation Company Snapshot
Table 14.16 Intel Corporation Key Developments
Table 14.17 Symantec Corporation Company Snapshot
Table 14.18 Symantec Corporation Key Developments
Table 14.19 Trend Micro Incorporated Company Snapshot
Table 14.20 Trend Micro Incorporated Key Developments
Table 14.21 Verizon Communications Company Snapshot
Table 14.22 Verizon Communications Key Developments
Table 14.23 Lockheed Martin Corporation Company Snapshot
Table 14.24 Selected Lockheed Martin Corporation Cyber Security Contracts / Projects / Programmes (Date, Country, Value US$m, Product, Details)
Table 14.25 Northrop Grumman Corporation Company Snapshot
Table 14.26 Selected Northrop Grumman Corporation Cyber Security Contracts / Projects / Programmes (Date, Country, Value US$m, Details)
Table 14.27 Palo Alto Networks Inc. Company Snapshot
Table 14.28 Other Companies Involved in the Cyber Security Market 2017 (Company, Estimated Sales in the Market $USm, Location)
List of Figures
Figure 1.1: Global Cyber Security Market Segmentation Overview
Figure 1.2 Example of Cyber Security Market by Regional Market Share Forecast 2017, 2027 (% Share)
Figure 1.3 Example of National vs. Global Cyber Security Market CAGR Forecast 2017-2027 (CAGR %)
Figure 2.1 Common Stages of Cyber Attacks
Figure 3.1 Cyber Security Market Drivers
Figure 3.2 Cyber Security Market Restraints
Figure 3.3 Cyber Security Market Challenges
Figure 4.1 Value Chain Analysis
Figure 5.1 Porter’s Five Forces Analysis
Figure 6.1 Global Cyber Security Risk and Compliance Management Submarket Forecast 2017-2027 (US$m)
Figure 6.2 Global Cyber Security UTM Submarket Forecast 2017-2027 (US$m)
Figure 6.3 Global Cyber Security Security Incident Management Submarket Forecast 2017-2027(U$m)
Figure 6.4 Global Cyber Security IAM Submarket Forecast 2017-2027(US$m)
Figure 6.5 Global Cyber Security Encryption Submarket Forecast 2017-2027(US$m)
Figure 6.6 Global Cyber Security IPS Submarket Forecast 2017-2027(US$m)
Figure 6.7 Global Cyber Security Other Submarket Forecast 2017-2027(US$m)
Figure 6.8 North America Cyber Security Risk and Compliance Management Solution Submarket Forecat 2017-2027(US$m)
Figure 6.9 Europe Cyber Security Risk and Compliance Management Solution Submarket Forecast 2017-2027(US$m)
Figure 6.10 Asia-Pacific Cyber Security Risk and Compliance Management Solution Submarket Forecast 2017-2027(US$m)
Figure 6.11 LAMEA Cyber Security Risk and Compliance Management Solution Submarket Forecast 2017-2027(US$m)
Figure 6.12 North America Cyber Security UTM Solution Forecast 2017-2027(US$m)
Figure 6.13 Europe Cyber Security UTM Solution Forecast 2017-2027(US$m)
Figure 6.14 Asia-Pacific Cyber Security UTM Solution Forecast 2017-2027(US$m)
Figure 6.15 LAMEA Cyber Security UTM Solution Forecast 2017-2027(US$m)
Figure 6.15 North America Cyber Security Security Incident Management Solution Forecast 2017-2027(U$m)
Figure 6.17 Europe Cyber Security Security Incident Management Solution Forecast 2017-2027(U$m)
Figure 6.18 Asia-Pacific Cyber Security Security Incident Management Solution Forecast 2017-2027(US$m)
Figure 6.19 LAMEA Cyber Security Security Incident Management Solution Forecast 2017-2027(US$m)
Figure 6.20 North America Cyber IAM Solution Forecast 2017-2027(US$m)
Figure 6.21 Europe Cyber Security IAM Solution Forecast 2017-2027(US$m)
Figure 6.22 Asia-Pacific Cyber Security IAM Solution Forecast 2017-2027(US$m)
Figure 6.23 LAMEA Cyber Security IAM Solution Forecast 2017-2027(US$m)
Figure 6.24 North America Cyber Security Encryption Solution Forecast 2017-2027(US$m)
Figure 6.25 Europe Cyber Security Encryption Solution Forecast 2017-2027(US$m)
Figure 6.26 Asia-Pacific Cyber Security Encryption Solution Forecast 2017-2027(US$m)
Figure 6.27 LAMEA Cyber Security Encryption Solution Forecast 2017-2027(US$m)
Figure 6.28 North America Cyber Security IPS Solution Forecast 2017-2027(US$m)
Figure 6.29 Europe Cyber Security IPS Solution Forecast 2017-2027(US$m)
Figure 6.30 Asia-Pacific Cyber Security IPS Solution Forecast 2017-2027(US$m)
Figure 6.31 LAMEA Cyber Security IPS Solution Forecast 2017-2027(US$m)
Figure 6.32 North America Cyber Security Other Solution Forecast 2017-2027(US$m)
Figure 6.33 Europe Cyber Security Other Solution Forecast 2017-2027(US$m)
Figure 6.34 Asia-Pacific Cyber Security Other Solution Forecast 2017-2027(US$m)
Figure 6.35 LAMEA Cyber Security Other Solution Forecast 2017-2027(US$m)
Figure 6.36 Global Cyber Security Solution Submarket Share Forecast 2017 (% Share)
Figure 6.37 Global Cyber Security Solution Submarket Share Forecast 2022 (% Share)
Figure 6.38 Global Cyber Security Solution Submarket Share Forecast 2017 (% Share)
Figure 6.38 Global Cyber Security Solution Submarket Share Forecast 2022 (% Share)
Figure 6.39 Global Cyber Security Solution Submarket Share Forecast 2027 (% Share)
Figure 7.1 Global Cyber Security Professional Submarket Forecast 2017-2027 (US$m)
Figure 7.2 Global Cyber Security Managed Submarket Forecast 2017-2027 (US$m)
Figure 7.3 North America Cyber Security Professional Services Submarket Forecast 2017-2027(US$m)
Figure 7.4 Europe Cyber Security Professional Services Submarket Forecast 2017-2027(US$m)
Figure 7.5 Asia-Pacific Cyber Security Professional Services Submarket Forecast 2017-2027(US$m)
Figure 7.6 LAMEA Cyber Security Professional Services Submarket Forecast 2017-2027(US$m)
Figure 7.7 North America Cyber Security Managed Services Forecast 2017-2027(US$m)
Figure 7.8 Europe Cyber Security Managed Services Forecast 2017-2027(US$m)
Figure 7.9 Asia-Pacific Cyber Security Managed Services Forecast 2017-2027(US$m)
Figure 7.10 LAMEA Cyber Security Managed Services Forecast 2017-2027(US$m)
Figure 7.11 Global Cyber Security Services Submarket Share Forecast 2017 (% Share)
Figure 7.12 Global Cyber Security Services Submarket Share Forecast 2022 (% Share)
Figure 7.13 Global Cyber Security Services Submarket Share Forecast 2027 (% Share)
Figure 8.1 Global Cyber Security Cloud Submarket Forecast 2017-2027 (US$m)
Figure 8.2 Global Cyber Security On-Premises Submarket Forecast 2017-2027 (US$m)
Figure 8.3 North America Cyber Security Cloud Based Submarket Forecast 2017-2027(US$m)
Figure 8.4 Europe Cyber Security Cloud Based Submarket Forecast 2017-2027(US$m)
Figure 8.5 Asia-Pacific Cyber Security Cloud Based Submarket Forecast 2017-2027(US$m)
Figure 8.6 LAMEA Cyber Security Cloud Based Submarket Forecast 2017-2027(US$m)
Figure 8.7 North America Cyber Security On-Premises Forecast 2017-2027(US$m)
Figure 8.8 Europe Cyber Security On-Premises Forecast 2017-2027(US$m)
Figure 8.9 Asia-Pacific Cyber Security On-Premises Forecast 2017-2027(US$m)
Figure 8.10 LAMEA Cyber Security On-Premises Forecast 2017-2027(US$m)
Figure 9.1 Global Cyber Security Deployment Type Submarket Share Forecast 2017 (% Share)
Figure 9.2 Global Cyber Security Deployment Type Submarket Share Forecast 2022 (% Share)
Figure 9.3 Global Cyber Security Deployment Type Submarket Share Forecast 2027 (% Share)
Figure 9.4 Global Cyber Security Large Enterprises Submarket Forecast 2017-2027 (US$m)
Figure 9.5 Global Cyber Security SMEs Submarket Forecast 2017-2027 (US$m)
Figure 9.6 North America Cyber Security Large Enterprises Submarket Forecast 2017-2027(US$m)
Figure 9.7 Europe Cyber Security Large Enterprises Submarket Forecast 2017-2027(US$m)
Figure 9.8 Asia-Pacific Cyber Security Large Enterprises Submarket Forecast 2017-2027(US$m)
Figure 9.9 LAMEA Cyber Security Large Enterprises Submarket Forecast 2017-2027(US$m)
Figure 9.10 North America Cyber Security SMEs Forecast 2017-2027(US$m)
Figure 9.11 Europe Cyber Security SMEs Forecast 2017-2027(US$m)
Figure 9.12 Asia-Pacific Cyber Security SMEs Forecast 2017-2027(US$m)
Figure 9.13 LAMEA Cyber Security SMEs Forecast 2017-2027(US$m)
Figure 10.1 Global Cyber Security User Type Submarket Share Forecast 2017 (% Share)
Figure 10.2 Global Cyber Security User Type Submarket Share Forecast 2022 (% Share)
Figure 10.3 Global Cyber Security User Type Submarket Share Forecast 2027 (% Share)
Figure 10.4 Global Cyber Security Aerospace & Defense Submarket Forecast 2017-2027 (US$m)
Figure 10.5 Global Cyber Security BFSI Submarket Forecast 2017-2027 (US$m)
Figure 10.6 Global Cyber Security Public Sector Submarket Forecast 2017-2027(US$m)
Figure 10.7 Global Cyber Security Retail Submarket Forecast 2017-2027(US$m)
Figure 10.8 Global Cyber Security Healthcare Submarket Forecast 2017-2027(US$m)
Figure 10.9 Global Cyber Security IT & Telecom Submarket Forecast 2017-2027(US$m)
Figure 10.10 Global Cyber Security Energy & Utlities Submarket Forecast 2017-2027(US$m)
Figure 10.11 Global Cyber Security Manufacturing Submarket Forecast 2017-2027(US$m)
Figure 10.12 Global Cyber Security Others Submarket Forecast 2017-2027(US$m)
Figure 10.13 North America Cyber Security Aerospace & Defense Submarket Forecast 2017-2027(US$m)
Figure 10.14 Europe Cyber Security Aerospace & Defense Submarket Forecast 2017-2027(US$m)
Figure 10.15 Asia-Pacific Cyber Security Aerospace & Defense Submarket Forecast 2017-2027(US$m)
Figure 10.16 LAMEA Cyber Security Aerospace & Defense Submarket Forecast 2017-2027(US$m)
Figure 10.17 North America Cyber Security BFSI Forecast 2017-2027(US$m)
Figure 10.18 Europe Cyber Security BFSI Forecast 2017-2027(US$m)
Figure 10.19 Asia-Pacific Cyber Security BFSI Forecast 2017-2027(US$m)
Figure 10,20 LAMEA Cyber Security BFSI Forecast 2017-2027(US$m)
Figure 10.21 North America Cyber Security Public Sector Forecast 2017-2027(US$m)
Figure 10.22 Europe Cyber Security Public Sector Forecast 2017-2027(US$m)
Figure 10.23 Asia-Pacific Cyber Security Public Sector Solution Forecast 2017-2027(US$m)
Figure 10.24 LAMEA Cyber Security Public Sector Forecast 2017-2027(US$m)
Figure 10.25 North America Cyber Retail Forecast 2017-2027(US$m)
Figure 10.26 Europe Cyber Security Retail Forecast 2017-2027(US$m)
Figure 10.27 Asia-Pacific Cyber Security Retail Forecast 2017-2027(US$m)
Figure 10.28 LAMEA Cyber Security Retail Forecast 2017-2027(US$m)
Figure 10.29 North America Cyber Security Healthcare Forecast 2017-2027(US$m)
Figure 10.30 Europe Cyber Security Healthcare Forecast 2017-2027(US$m)
Figure 10.31 Asia-Pacific Cyber Security Healthcare Forecast 2017-2027(US$m)
Figure 10.32 LAMEA Cyber Security Healthcare Forecast 2017-2027(US$m)
Figure 10.33 North America Cyber Security IT and Telecom Forecast 2017-2027(US$m)
Figure 10.34 Europe Cyber Security IT and Telecom Forecast 2017-2027(US$m)
Figure 10.35 Asia-Pacific Cyber Security IT and Telecom Forecast 2017-2027(US$m)
Figure 10.36 LAMEA Cyber Security IT and Telecom Forecast 2017-2027(US$m)
Figure 10.37 North America Cyber Security Energy and Utilities Forecast 2017-2027(US$m)
Figure 10.38 Europe Cyber Security Energy and Utilities Forecast 2017-2027(US$m)
Figure 10.39 Asia-Pacific Cyber Security Energy and Utilities Forecast 2017-2027(US$m)
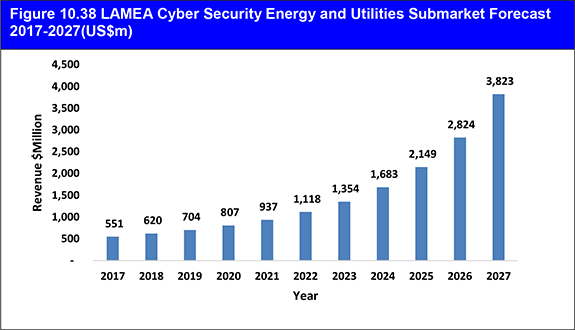
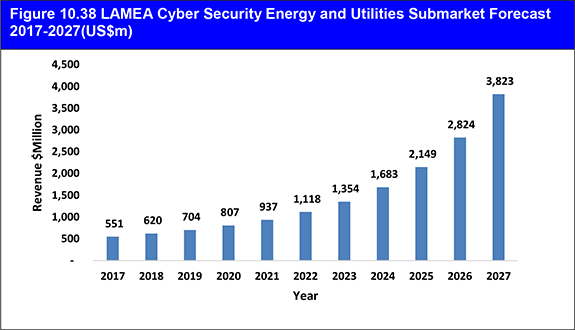
Figure 10.40 LAMEA Cyber Security Energy and Utilities Forecast 2017-2027(US$m)
Figure 10.41 North America Cyber Security Manufacturing Forecast 2017-2027(US$m)
Figure 10.42 Europe Cyber Security Manufacturing Forecast 2017-2027(US$m)
Figure 10.43 Asia-Pacific CyberSecurity Manufacturing Forecast 2017-2027(US$m)
Figure 10.44 LAMEA Cyber Security Manufacturing Forecast 2017-2027(US$m)
Figure 10.45 North America Cyber Security Other Industry Vertical Forecast 2017-2027(US$m)
Figure 10.46 Europe Cyber Security Other Industry Vertical Forecast 2017-2027(US$m)
Figure 10.47 Asia-Pacific Cyber Security Other Industry Vertical Forecast 2017-2027(US$m)
Figure 10.48 LAMEA Cyber Security Other Industry Vertical Forecast 2017-2027(US$m)
Figure 10.49 Global Cyber Security Industry Vertical Submarket Share Forecast 2017 (% Share)
Figure 10.50 Global Cyber Security Industry Vertical Submarket Share Forecast 2022 (% Share)
Figure 10.51 Global Cyber Security Industry Vertical Submarket Share Forecast 2027 (% Share)
Figure 11.1 North American Cyber Security Market Revenue, 2017-2027(US$m)
Figure 11.2 North American Cyber Security Market Revenue, By Country, 2017-2027(US$m)
Figure 11.3 Europe Cyber Security Market Revenue, 2017-2027(US$m)
Figure 11.4 Asia-Pacific Cyber Security Market Revenue, 2017-2027(US$m)
Figure 11.5 LAMEA Cyber Security Market Revenue, 2017-2027(US$m)
Figure 12.1 Leading 9 National Cyber Security Markets Share Forecast 2017 (% Share)
Figure 12.2 Leading 9 National Cyber Security Markets Share Forecast 2027 (% Share)
Figure 12.3 Leading 9 National Cyber Security Markets Cumulative Sales Share Forecast 2017-2027 (% Share)
Figure 12.4 China Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.5. France Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.6 France Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.7 France Cyber Security Agency (ANSSI) Organisational Structure 2017
Figure 12.8 Japan Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.9 Japan Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.10 Russia Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.11 Russia Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.12 U.S. Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.13 U.S. Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.14 U.S. Government and Military Cyber Security Organisations
Figure 12.15 UK Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.16 UK Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.17 UK National Cyber Security Programme Spending by Segments Share 2017-2017 (Share %)
Figure 12.18 South Korea Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.19 Israel Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.20 Israel Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 12.21 Saudi Arabia Cyber Security Market Forecast 2017-2027 (US$m)
Figure 12.22 Saudi Arabia Cyber Security Market Share Forecast 2017, 2027 (% Share)
Figure 14.1 Top 6 Cyber Security Company Market Share Analysis 2016 (%)
Figure 14.2 Dell EMC Net Sales, 2013-2015
Figure 14.3 Dell EMC, Business Segment, 2015(%)
Figure 14.4 Dell EMC, Geography, 2015(%)
Figure 14.5 Cisco Systems Net Sales, 2014-2016
Figure 14.6 Cisco Systems, Business Segment, 2016(%)
Figure 14.7 Cisco Systems, Geography, 2016(%)
Figure 14.8 FireEye Incorporated Net Sales, 2013-2015
Figure 14.9 FireEye Incorporated, Business Segment, 2015(%)
Figure 14.10 FireEye Incorporated, Geography, 2015(%)
Figure 14.11 HPE Net Sales, 2013-2015
Figure 14.12 HPE, Business Segment, 2015(%)
Figure 14.13 HPE, Geography, 2015(%)
Figure 14.14 IBM Net Sales, 2013-2015
Figure 14.15 IBM, Business Segment, 2015(%)
Figure 14.16 IBM, Geography, 2015(%)
Figure 14.17 Sophos Net Sales, 2015-2016
Figure 14.18 Sophos, Business Segment, 2016(%)
Figure 14.19 Sophos, Geography, 2016(%)
Figure 14.20 Intel Corporation Net Sales, 2013-2015
Figure 14.21 Intel Corporation, Business Segment, 2015(%)
Figure 14.22 Intel Corporation, Geography, 2015(%)
Figure 14.23 Symantec Corporation Net Sales, 2014-2016
Figure 14.24 Symantec Corporation, Business Segment, 2016(%)
Figure 14.25 Symantec Corporation, Geography, 2016(%)
Figure 14.26 Trend Micro Incorporated Net Sales, 2013-2015
Figure 14.27 Verizon Communications Net Sales, 2014-2016
Figure 14.28 Verizon Communications, Business Segment, 2016(%)
Figure 14.29 Verizon Communications, Geography, 2016(%)
Figure 14.30 Lockheed Martin Corporation Net Sales, 2014-2016
Figure 14.31 Lockheed Martin Corporation, Business Segment, 2016(%)
Figure 14.32 Northrop Grumman Corporation Net Sales, 2014-2016
Figure 14.33 Northrop Grumman Corporation, Business Segment, 2016(%)
Figure 14.34 Palo Alto Networks, Inc Net Sales, 2014-2016
Figure 14.35 Palo Alto Networks, Inc, Business Segment, 2016(%)
Figure 14.36 Palo Alto Networks, Inc, Geography, 2016(%)
Figure 15.1 Top Impacting Factors
Figure 15.2 Winning strategies
Figure 15.3 Winning strategies analysis
Figure 15.4 Growth Potential
ACE Group
ADACOM
Airbus
Airbus Defence and Space
Akamai Technologies
AlienVault
Alion Science and Technology
AT&T
Avast
AVG Technologies
BAE Systems
Bangladesh Bank
Baraccuda Networks
Barbaricum LLC
Baum, Romstedt Technology Research Corp.
BitDefender
Blue Coat Systems
Boeing Defense, Space & Security
Booz Allen Hamilton Inc.
Booz Allen Hamilton Inc.
Bull
Capita
Carahsoft Technology
Check Point Software
Cisco Systems
CloudLock
CommVerge Solutions
Crowdstrike
Cyber Defense Information Assurance
CyberArk
Cyberoam
Darktrace
Dell EMC
Dell Security
Deloitte Touche Tohmatsu Ltd
Digital Shadows
Ernst&Young Global Ltd
ESET
Exelis, Inc.
F5 Networks
FireEye
Fortinet
F-Secure
Gemalto
General Dynamics Corporation
Georgia Tech Applied Research Corporation
Guidance Software
Hewlett Packard Enterprise (HPE)
Hitachi
Honeywell
Honeywell Process Solutions
Huawei
IBM Corporation
iboss Cybersecurity
Identity Theft Guard Solutions LLC
Ingram Micro
Intel Corporation
Intel Security
Isis Defence
Juniper Networks
Kaspersky Lab
KIOSK Information Systems (KIOSK)
KPMG
Kudu Dynamics LLC
L-3 Communications
LANDesk Software
Leidos Inc
Lockheed Martin Corporation
LogRhythm
MacAulay-Brown, Inc.
Malwarebytes Anti-Malware
ManTech Advance Systems International, Inc.
McAfee
Micro Focus (Novell)
North American Electric Reliability Corporation (NERC)
Northrop Grumman Corporation
Northrop Grumman Information and Technology, Inc
Northrop Grumman Systems Corporation
Nozomi Networks
Oak Ridge
Oce
Onyx Healthcare
Optiv Security
Oracle
Orange
Pala Alto Networks Inc.
Panda Security
PricewaterhouseCoopers (PWC)
Professional Project Services Inc.
ProofPoint
Radware
Raytheon
Raytheon BBN Technologies Corp
Resilient Systems
Rockwell Automation
root9B
RSA Security
RUAG
Safran
Sierra Nevada Corp
SMS Data Products Group Inc.
Solers Inc.
SonicWall (Dell)
Sophos Ltd.
SophosLabs
Splunk
SurfRight
Symantec Corporation
TASC, Inc.
Telos Corporation
Thales Group
The SSL Store
Trend Micro
Tripwire
Vencore Labs Inc
Veracode
Verisign
Verizon Communications
Verizon Enterprise Solutions
Visa, Inc.
VMware
Vormetric
WatchGuard
Waterfall Security Solutions
Willis Group Holdings
Wyle Laboratories, Inc.
X Technologies, Inc
Organisations Mentioned
Agence National de la Security des Systemes d’Information (ANSSI)
China CERT
Chinese Ministry of National Defence
European Commission
Federal Energy Regulatory Commission (FERC)
French Ministry of Defence
French Ministry of Interior
General Office of the Communist Party of China (CPC) Central Committee
General Office of the State Council
International Telecommunication Union (ITU)
INTERPOL
Japanese Ministry of Defence
Japanese National Centre of Incident Readiness and Strategy for Cyber Security (NISC)
Japan's Ministry of Internal Affairs and Communications
Ministry of Economy, Trade and Industry (METI)
Ministry of internal Affairs and Communications (MIC)
Ministry of State Security
National Institute of Standards and Technology (NIST)
National Police Agency
People’s Liberation Army (PLA)
Ponemon Institute
Russia’s 5th Dimension Cyber Army
Russian Ministry of Defence
Stockholm International Peace Research Institute (SIPRI)
The Control Systems Security Centre (CSSC)
The Information Technology Promotion Agency (IPA)
The National Institute of Information and Communications Technology (NICT)
United Nations
US Army
US Cyber Mission Force
US Defense Advanced Research Projects Agency (DARPA)
US Defense Logistics Agency
US DHS
US Marine Corps Enterprise Network
US Navy
World Economic Forum